

“Protocols – A sequence of operations that ensure protection of data. Used with a communications protocol, it provides secure delivery of data between two parties. The term generally refers to a suite of components that work in tandem. Secure client portal” – PC Magazine
Data Center Certificates:
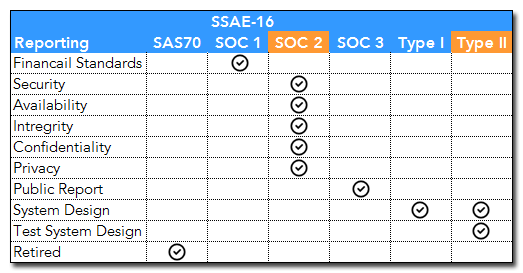
a. SOC 2 Type II – This is an enhancement to the current standard for Reporting on Controls at a Service Organization, the SAS70 Type II CERT. The changes made to the standard will bring companies in the U.S. up to date with new international service organization reporting standards, the ISAE 3402. The adjustments made from SAS 70 to SSAE 16 will help companies in the U.S. compete on an international level.
b. Within the SOC 2 Type II report, our data center requested testing on the following guide lines, and the data center met or exceeded the guide lines for the following:
ICFiles utilizes industry leading hardware and software solutions.
All data that interacts with the database is fully validated, filtered, controlled and whitelisted before being used in any database query.
All user input to the database is “escaped” to prevent injection code from operating on the database.
a. Your data is first encrypted upon upload with a DigiCert SSL (Secure Sockets Layer) 4096 Bit SHA2 certificate. Then, your data upon arriving at the Windows Server is re-encrypted using AES 128/256 encrypt. APSEncrypt is an Active Server component that brings security to your applications through encryption. This component can be used in an ASP/ASP.NET or VB environment on Windows 2003/2008/2012/2016/Vista/7/8/10.
b. While backing up your data our Cloud, servers keep your data encrypted.
c. Downloads work in the reverse order and are always encrypted.
d. SSL Transfer is always forced.
All file names are altered with randomly generated code and all file data are hidden from the World Wide Web. Unauthorized access is impossible.
Your data is protected by your username and password under our guidelines for strong protection. If a logon attempt using your password is used more than a certain number of times, the system will block your account and you will need to follow the reset password procedure. Your IP address will be recorded and your account will have a temporary password emailed to the contact. Once you have signed on for the first time you will be asked to reset your password. All passwords have one way encryption and can never be retrieved. This is a bulletproof process for securing your data files.
Your data files are scanned on arrival and departure with McAfee Virus Scan Enterprise & Anti Spyware Enterprise. McAfee utilizes industry-leading proactive detection to keep your company data safe from existing and emerging threats while keeping false positives to a minimum. Secure client portal.
ICFiles keeps a complete log on all current file activity, giving our clients complete history of all their clients’ documents. This history file can be downloaded.
Fiber Speed – 15x times faster. Your upload and download speeds will only be limited by your ISP and your location in the www. Note: For clients with ISPs providing higher than 10Mbps up or down, your connection can also be limited by routing servers on the www.
Multiple Fiber carriers in building: Comcast, Level3, NIT America, TeliaSonera, Equinix, Telefonica, and Time Warner.
ICFiles, a Secure Client Portal, is scanned for vulnerabilities regularly and is tested and verified by 3rd party security analysts.




